How to delete Sync.malwareprotecionlive.com from windows pc effectively:

Sync.malwareprotecionlive.com is basically identified as a unwanted pop-up sites that can infect and cause severe harm on to all your installed web browsers. Mainly Sync.malwareprotecionlive.com comes from the family of the browser hijacker whose main aim is to hijack and to take control on to your installed web browsers. Once the browser get infected with it result to change the DNS settings and modify the default settings of your commonly used web browsers such as Mozilla Firefox, Internet Explorer, Google Chrome and so on. Moreover it is also refer to as the potentially unwanted program (PUP) and displays tons of annoying and irritating pop-up ads, banners, offers, deals, coupons etc within the system screen. It is also capable to deactivate the installed anti-virus program from the infected system and also crack the browser firewall security program too. Further, Sync.malwareprotecionlive.com also redirect all your web search to its domain site or to some other unknown suspicious websites. It also installs unknown and additional program like toolbar, add-on, extension, plugin etc on to your installed web browser. Therefore, for the safety of the browsers it is highly advised you to remove Sync.malwareprotecionlive.com at the earlier from infected web browsers.
On the other end, Sync.malwareprotecionlive.com is also capable to trace all your online activities and steal all your personal details. All these gathered information are further by pass it to the remote server to perform elicit tasks through it. It also weaken the speed of your Internet connection and pay extra loads on to it. Also block you to surf on to your favorite websites and bookmark sites. The performance of the system also degrade down and consumed huge amount of the system resources. Even corrupt all your files, data, folders etc that are stored within the system. Remove Sync.malwareprotecionlive.com as soon as possible from your computer.
Expert Recommendation:
Threat Assessment of Sync.malwareprotecionlive.com :
Sync.malwareprotecionlive.com is a deadly malware. Technically speaking, its a sub-routine or a smaller program which interrupts the current operations of system and try to deploy its own code with a unique property of replicating itself and changing the behavior according to the situation. Below here is a threat assessment of Sync.malwareprotecionlive.com as per the wilderness and the damage done by it.
Category
Sync.malwareprotecionlive.com has been categorized as a very deadly or critical infection which can infect a large no. of system at once.
Geographical distribution
It can affect a large number of system across the whole world simultaneously. It comes with a capability of spreading itself from system to system. Moreover it tries to target western countries since they have large number of internet users.
System Target
It generally target Windows PC. It can attack on any OS including XP, W 7, W 8, etc.
Infection capabilities
It can infect around 70-100 files at once. It can even target the entire machine and can also damage the network systems.
Above assessment clearly shows that Sync.malwareprotecionlive.com is a lethal malware. Any ignorance to them may cause you to face par thinking consequences therefore one should never risk on it and try to remove as soon as possible.
Consequences of Sync.malwareprotecionlive.com Infection (PC + Internet) :
Sync.malwareprotecionlive.com may have literally deadly consequences. Its consequences may be even invisible also. Your system might look like a good, neat and properly working system but it might be secretly sending your data and personal details to some one. Some of the major consequences of being attacked by Sync.malwareprotecionlive.com on your system as well as on your internet connection is discussed below.
Consequences On PC :
- Degrades the PC performance.
- Unnecessary error messages.
- Excessive boot time.
- Freezing of system which might lead to system crash, etc.
Consequences on Internet :
- Browser hijacking; Its kind of hacking the browser like Firefox, chrome, etc. by changing the homepage setting and URL,thus taking you to some fake and malicious website deliberately.
- Identity theft; Stealing your personal details like credit card number, passwords, etc. online is quite common and Sync.malwareprotecionlive.com can easily make you a victim of this.
- Unnecessary and annoying pop ups.
- Fake and malicious emails.
Above discussed are some of the major consequences of Sync.malwareprotecionlive.com attack . One may encounter lots of different and even more danger consequences. One should never ignore if any thing unusual happens to the system. To be safe, every one should go for a Sync.malwareprotecionlive.com removal tool as soon as any of the symptoms is seen.
Software Note :
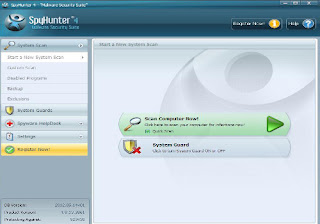
Demo version of automatic Sync.malwareprotecionlive.com removal tool is easily available over the internet. In demo version you can check the software features and working process of this application. Download and then install it on your PC. You can install it very easily in two – three simple steps without any problem. In the demo version, you can scan the entire PC after which a list of spyware, malware or infected files and folders is shown, but removal process cannot be preceded. So, for complete Sync.malwareprotecionlive.com removal, you need to purchase the licensed version of tool. In this version, easy as well as safe removal of spyware and other harmful files from your computer can be done in few simple steps. This tool supports all versions of windows operating system like windows 8, win 7, xp, vista, win 97, 98, 2000, 2003, windows server 2008.
User guide to remove Sync.malwareprotecionlive.com with Sync.malwareprotecionlive.com removal tool :
Step2: If you face any problem regarding installation of the software, either then use anther browser or restart your PC in safe mode with networking
Step3: After you finished installing the Software, scan your PC
Other Search Terms for Sync.malwareprotecionlive.com infection
Sync.malwareprotecionlive.com , How to remove Sync.malwareprotecionlive.com , get rid of Sync.malwareprotecionlive.com , steps to delete Sync.malwareprotecionlive.com , Sync.malwareprotecionlive.com automatic remove. uninstall Sync.malwareprotecionlive.com.




No comments:
Post a Comment