How to delete click.monetizer.info from windows pc effectively:

click.monetizer.info is defined as a malicious fake security alert pop-up virus. It has close relationship with dubious antivirus programs or other rogue malware. To get into your PC, it does not need any of your approval and does numbers of illegal activities to it. It replaces your default browser engine and settings. It is too much annoying and designed by online criminals with vicious intention. click.monetizer.info is so crafty to hide on computer that users are not supposed to take it out from computer easily. By changing the settings on web browsers, it is able to popup on to Google Chrome, Mozilla Firefox, Internet Explorer and Microsoft Edge randomly. When a pop-up occurs , you might experience a Fake Flash Player update, a Fake Media Player update or other social engineering scams.
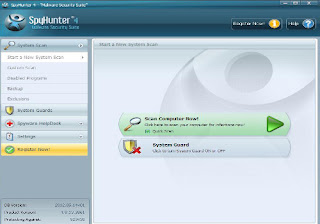
This click.monetizer.info is actually an ad-supported platform that working for nasty third-parties malware. It compromises the browsers with all kinds of unwanted pop-ups : fake alerts, coupons, discounts, programs update notification, sponsored links and also banners. And these causes web traffic. The ads from this domain are triggered by keywords. These keywords are often underlined by a red, green or blue color turn in to hyperlinks. click.monetizer.info creates many security problems that are associated to users inactivity in their computer. For example, it displays scam ads that redirect you to insecure websites, it over use CPU to make system sluggish, it corrupt the programs and force to buy its activation key with lots of money, it helps hijacker take over your web browser and hack accounts steal informations.
We can say that, click.monetizer.info is a risky adware which invades into computer silently without users permission and bundled with many free software. It traces your online activities for collecting your browsing behaviors. Thus, to make sure the security of your precious data, it's strongly advised to remove this adware out from computer immediately without any delay.
Expert Recommendation:
- During the internet browsing when you open any malicious web page which contains various malicious agents that enters into your PC and effects.
- When you open a link, emails, attachment etc. which is sent from a untrusted source .
- Someone else's USB drives plugging into your computer which contains the malicious files, folder, application etc. spreads click.monetizer.info spyware into your computer.
- During the internet browsing many types of pop-ups appear which contain many types of malicious sites and program. It tells you to follow the infected link to remove virus from your computer but actually itself a virus.
- Downloading movie, programs, games etc from the internet may contains click.monetizer.info spyware.
- Installation of unknown application on your windows PC. This program is actually types of click.monetizer.info spyware. So don't install any malicious program in your computer.
- “Unable to access the files and folders.”
- “Suspicious software activity is detected by click.monetizer.info spyware on your computer.”
- “Your computer is at high risk or use it at your own risk.”
- “There's suspicious software running on your PC. For more details, run a system file check.”
- “Computer slows down, perform scan.”
- “ Warning Running Trial version
- Click here to purchase the full version of the software and get full protection for your PC.”
click.monetizer.info , How to remove click.monetizer.info , get rid of click.monetizer.info , steps to delete click.monetizer.info , click.monetizer.info automatic remove. uninstall click.monetizer.info.



No comments:
Post a Comment