How to delete HTML:Phishing-IC from windows pc effectively:
HTML:Phishing-IC is detected as one of the harmful and malicious trojan that once injects within the user computer may results to cause lots of problems to the system. These trojan are mainly used to help the cyber criminal to do online fraud activities and infects the user computer very badly. On the other hand it is also capable to infects and cause harms to all the versions of the Window operating system that basically include Window XP, Window 7, Window 8 and Window Vista. Besides all these it also modify the system DNS settings and modify the installed web browser settings including its web home page too. It also opens the system backdoor gate to drop infected and malicious files on the system. As once this harmful program get installed within the system it start to perform the execution of its malicious files and thus distribute its harmful codes to entire parts of it. It is therefore very necessary to remove HTML:Phishing-IC from your computer without any delay.
HTML:Phishing-IC also collects all the web surfing activities of the user like web search, search queries, IP address, URL, web history and such more to forward all these details to the remote server. Even it also slow the performance of the system by the use of the huge system resources and usage of its memory and CPU space. Further, it also redirect your web search to its domain and other unknown suspicious websites to cause more harm to the system. So at the earlier you should remove HTML:Phishing-IC completely from your system.
Expert Recommendation:
3 User Testimonials :
“I was really shocked and scared after seeing the ransom message. I even started thinking of my some past mistakes and felling guilty. I restarted the system like hundred times in hope of happening something good but everything was waste. Thanks to the automatic HTML:Phishing-IC removal tool. It made every thing alright in just few clicks. Its really a great malware removal tool. “
Mary, Bern, Switzerland
“I had to wait for almost 10 minutes after switching on my system to boot. As the desktop appears, there were hell lot of error messages. I used many anti-HTML:Phishing-IC softwares but nothing good happened. At last, one of my friend suggested me automatic HTML:Phishing-IC removal tool. I used it and every problem to my system was resolved. It was now working like a new PC.”
Sur, L.A
“Automatic HTML:Phishing-IC removal tool is a life saver software. It made my PC like a new one.
Without scanning my friend's USB, I inserted it in my PC and made it perform like hell but HTML:Phishing-IC removal tool resolved every issue in just few clicks.”
Nikks, U.S.
Connects to Online Hacker :
Sitting somewhere in the world, may be hundreds or thousands miles away and controlling your entire system's activity is not a big deal for some advanced hackers. They can literally perform magic over the internet rather we should say black magic. You wont even get a single clue and your whole system will be exposed to them.
Hackers some how install HTML:Phishing-IC on you system through internet. Now as you open your system it gets activated and starts capturing your activities. Mostly they target to capture the keys pressed from your keyboard. This is done by an application called keylogger. A key logger is a small application which captures and records all the keys pressed from your keyboard and activities of a system and keeps on sending it to the the host hacker. Hence stealing your each and every password, credit card number, user names and other personal information. This is one of the most common ways to make some one a victim of identity theft and money laundering.
For a common skilled user, it is next to impossible to identify it. Therefore one has to be very careful while surfing internet. One should always go for an automatic HTML:Phishing-IC removal tool in order to be safe instead of manual method because removing HTML:Phishing-IC manually in quite impossible.
How HTML:Phishing-IC Enters windows PC :
HTML:Phishing-IC is detected as dangeous infection that spreads from one computer to another. It can copy itself and spread in your entire windows PC hard disk without the consent of users. It spreads very quickly in a short time period and effects your whole PC performance. Here are some of the possible ways through which it enters into your windows PC :
- During the internet browsing when you open any malicious web page which contains various malicious agents that enters into your PC and effects.
- When you open a link, emails, attachment etc. which is sent from a untrusted source .
- Someone else's USB drives plugging into your computer which contains the malicious files, folder, application etc. spreads HTML:Phishing-IC spyware into your computer.
- During the internet browsing many types of pop-ups appear which contain many types of malicious sites and program. It tells you to follow the infected link to remove virus from your computer but actually itself a virus.
- Downloading movie, programs, games etc from the internet may contains HTML:Phishing-IC spyware.
- Installation of unknown application on your windows PC. This program is actually types of HTML:Phishing-IC spyware. So don't install any malicious program in your computer.
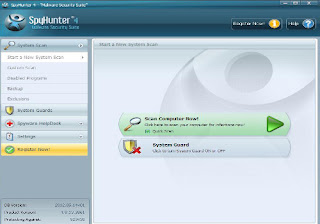
User guide to remove HTML:Phishing-IC with HTML:Phishing-IC removal tool :
Step2: If you face any problem regarding installation of the software, either then use anther browser or restart your PC in safe mode with networking
Step3: After you finished installing the Software, scan your PC
Other Search Terms for HTML:Phishing-IC infection
HTML:Phishing-IC , How to remove HTML:Phishing-IC , get rid of HTML:Phishing-IC , steps to delete HTML:Phishing-IC , HTML:Phishing-IC automatic remove. uninstall HTML:Phishing-IC.



No comments:
Post a Comment