How to delete usg.spiessummarizing.com from windows pc effectively:
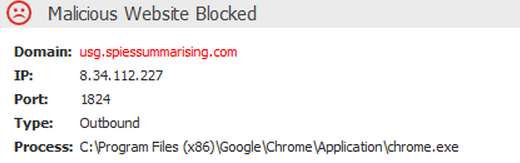
usg.spiessummarizing.com is identified as the risky and unsafe domain that cause lots of problems to your installed web browsers and even take complete control over it. It easily infects and hijacks the browser by the download of freeware program, opening of the Spam email attachments, p2p sharing of the files, use of the removable drives and such more. Moreover it is also promoted and hosted by the third party to advertise and promote their products and earn revenue from it. Also alter the settings of the installed web browser such as Google Chrome, Internet Explorer and Mozilla Firefox that also includes its web home page. Besides all these it also insists you to click on the sponsored links and fake ads. Therefore to overcome from such browser problems you should remove usg.spiessummarizing.com completely from your web browser.
usg.spiessummarizing.com also infects and corrupts your stored data, files and documents and thus prevent you to gain access on it. Further, it often redirect your web search to its domain and other suspicious websites to add more spyware and threats to it. Thus, it also block you from accessing your favorite websites and crack down the browser firewall. Add useful and unknown program on the web browser such as extension, plugin, add-on, toolbar etc without the concern of the user. Its effects also change the essential settings of the system like registry files, task manager, exe files, Window editor and such more that cause problem to operate on it. So it is strongly advised you to remove usg.spiessummarizing.com as soon as possible from your computer.
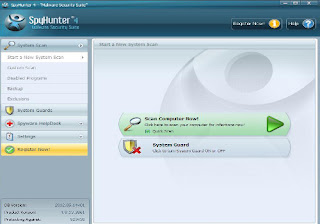
Expert Recommendation:
- It attaches itself into the memory and then infects all the computer files. It can modify the code itself and can change the subject or body of your email. Sometimes It carries the other virus program which makes it more lethal.
- It has some special ability to infect your different computer partition and master boot record also. These all changes may lead to abrupt functioning of the entire PC making it slow and sluggish in performance.
- Delete files when you want to run it and makes changes in your computer volume and creates more than one partitions.
- Infects system files extensions like .com, .exe. .sys, .bin , .pif and other file extensions and even increase and decrease the size of the file automatically .
- when you open the internet then browser does not open your default home page, it redirects to unsafe and malicious websites. Internet browsing speed becomes slower.
- sometimes when you starts your windows PC and can not access your computer data and it gets locked.
- Your computer desktop setting changes automatically and various types of unwanted shortcuts appear on your desktop.
- you will notice that your PC performance became slower and it takes time during the system start and shutdown.
- antivirus programs don't work properly and it has been disabled. It becomes unresponsive and unable to detect the infections. You can not install a new antivirus program in your computer.
- PC is restarting itself after every now and then and lastly it becomes crashed.
- All types of pop up messages and advertising notifies that the PC is infected and needs protection.
- Lots of application starts automatically when you start your computer and sometime when you open any application then it does not work properly.
usg.spiessummarizing.com , How to remove usg.spiessummarizing.com , get rid of usg.spiessummarizing.com , steps to delete usg.spiessummarizing.com , usg.spiessummarizing.com automatic remove. uninstall usg.spiessummarizing.com.


No comments:
Post a Comment