How to delete PCWebStat.com from windows pc effectively:

PCWebStat.com is an unwanted browser hijacker that can infects almost all types of web browsers available in your system. It has ability to bypass the examination of all reputed removal tool. In fact it installs risky plug-in without your consent and monitors your using activities on the computer system. PCWebStat.com is particularly created to endorse nasty content and change the real element of your search engine. The current search engine of the your web browsers will be changed randomly with a malevolent one which is actually hard to amend. It alters current homepage and search engine settings and harass almost all types of browsers like Internet Explorer, Apple Safari and Google Chrome etc.
PCWebStat.com display insecure search results i.e. full of in-textual links and advertisements. It publishes or works just similar to its sponsored Internet provider like Google and Msn but the tasks is just opposite. It is designed by the cyber hackers to promote commercials and precarious links. Afterwards, search engine will actually display unsafe and unreliable search results. In addition, it mainly targets your search engine provider to plug on lots of vicious things, like installs apps or toolbar or other unwanted programs. That's why, if you are suffering from these activities on your system, then immediately remove PCWebStat.com as it seen.
Expert Recommendation:
PCWebStat.com is a fatal threat and remove it as soon as possible. To get rid of it from windows pc, download
PCWebStat.com removal tool
Threat Assessment of PCWebStat.com :
PCWebStat.com is a deadly malware. Technically speaking, its a sub-routine or a smaller program which interrupts the current operations of system and try to deploy its own code with a unique property of replicating itself and changing the behavior according to the situation. Below here is a threat assessment of PCWebStat.com as per the wilderness and the damage done by it.
Category
PCWebStat.com has been categorized as a very deadly or critical infection which can infect a large no. of system at once.
Geographical distribution
It can affect a large number of system across the whole world simultaneously. It comes with a capability of spreading itself from system to system. Moreover it tries to target western countries since they have large number of internet users.
System Target
It generally target Windows PC. It can attack on any OS including XP, W 7, W 8, etc.
Infection capabilities
It can infect around 70-100 files at once. It can even target the entire machine and can also damage the network systems.
Above assessment clearly shows that PCWebStat.com is a lethal malware. Any ignorance to them may cause you to face par thinking consequences therefore one should never risk on it and try to remove as soon as possible.
Consequences of PCWebStat.com Infection (PC + Internet) :
PCWebStat.com may have literally deadly consequences. Its consequences may be even invisible also. Your system might look like a good, neat and properly working system but it might be secretly sending your data and personal details to some one. Some of the major consequences of being attacked by PCWebStat.com on your system as well as on your internet connection is discussed below.
Consequences On PC :
- Degrades the PC performance.
- Unnecessary error messages.
- Excessive boot time.
- Freezing of system which might lead to system crash, etc.
Consequences on Internet :
- Browser hijacking; Its kind of hacking the browser like Firefox, chrome, etc. by changing the homepage setting and URL,thus taking you to some fake and malicious website deliberately.
- Identity theft; Stealing your personal details like credit card number, passwords, etc. online is quite common and PCWebStat.com can easily make you a victim of this.
- Unnecessary and annoying pop ups.
- Fake and malicious emails.
Above discussed are some of the major consequences of PCWebStat.com attack . One may encounter lots of different and even more danger consequences. One should never ignore if any thing unusual happens to the system. To be safe, every one should go for a PCWebStat.com removal tool as soon as any of the symptoms is seen.
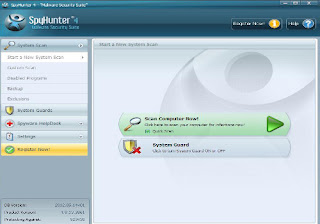
Automatic Tool Software Features :
Automatic PCWebStat.com removal tool is very safe and powerful anti-spyware application which protects your system from PCWebStat.com spyware and other with the help of its real time protection. Some important features of this application:
- Quick, complete and custom scanning - It scans your complete hard disk, removable drives, memory, registry, individuals folders etc .
- Detect and Remove - spyware , malware, adware, trojans, worms, keyloggers, hijackers and some other types of threat.
- Real-time Blocking – it provides you the facilities of real-time blocking of threat which prevents your computer from harmful software installation or re- installation.
- Automatic Threat update – fast and continuous threat updates are downloaded and installed automatically which protects your PC from different types of spyware.
- Easy and simple user interface – very interactive and user friendly interface where you can operate the tool without any help.
- Efficient support service : if you are facing the problem when you use the application then you can contact the customer support team where you can get the solution of your problem easily in few minutes.
- Operating system compatibility : it is compatible with the all windows versions like windows 7, win xp, vista, win 97, 98,2000, 2003, windows server 2008.

User Guide- To delete PCWebStat.com infections completely :
Below you can find out few simple steps that states you how to remove PCWebStat.com related infections from affected Windows PC. These steps will guide you throughout the process providing you technical help especially for those who don't have much knowledge about the computers.
Step 1.
First of all download and install the application properly after that open the application. When the main interface of the application will open then you will see the button “Scan computer”. Click on this button to start the scan for PCWebStat.com spyware in your pc.
Step 2.
After finishing the scanning process it will see the list of threats and infected items. When you select any one of them then you can see the details about the infected items and how much it is harmful.
Step 3.
With the help of “Spyware Help Desk ” you can easily find out the details related to the spyware and malware items which is found in your PC.
Step 4.
You can block all infected item with the help of “System Guard” to make you safe from spyware and malware.
User guide to remove PCWebStat.com with PCWebStat.com removal tool :
Step2: If you face any problem regarding installation of the software, either then use anther browser or restart your PC in safe mode with networking
Step3: After you finished installing the Software, scan your PC
Other Search Terms for PCWebStat.com infection
PCWebStat.com , How to remove PCWebStat.com , get rid of PCWebStat.com , steps to delete PCWebStat.com , PCWebStat.com automatic remove. uninstall PCWebStat.com.









No comments:
Post a Comment