How to delete Smartinf.ru from windows pc effectively:

Smartinf.ru is a browser hijacker. It is a vicious redirection used by criminals to take control of your web browser. Once infected,it will change the default setting to redirect you to other malicious websites. And after the redirection, Smartinf.ru virus maker will monitor your online activities to collect your confidential information such as banking account and password, completely endanger your property and privacy. Moreover, it will also degenerate your PC performance in many aspects, such as decelerating the network speed, harassing you with annoying pop-up ads, dropping malicious files into your PC etc.
Major objective of Smartinf.ru virus type is the scanning people's requests. This malicious and intrusive tool slithers its way into your system through tricky and finesse and then make a complete mess. Smartinf.ru usually sneaks in undetected with the help of the old but gold methods of invasion. More often than not, it hitches a ride with freeware or hides behind Spam email attachments, corrupted links, or websites. However, its most preferred and most commonly used way of infiltration involves the tool posing as a bogus system or program update.
Here, we have some common symptoms of Smartinf.ru. And they are :
- Pop-up ads
- Unwanted messages
- Search redirecting
- Seeing a search engine that looks like Google, but with an unfamiliar URL or logo
- Unknown search engine in a browser
- Changed Google search results
In other words, we can say that Smartinf.ru is a fake and bogus search website, that may try to look and feel, just like any other regular Internet search engine. It is capable of modifying web browser settings without users' consent or asking for any permission. If you don't want to face these problems, you are highly recommended to delete Smartinf.ru as soon as possible.
Expert Recommendation:
Smartinf.ru is a fatal threat and remove it as soon as possible. To get rid of it from windows pc, download
Smartinf.ru removal tool
Consequences of Smartinf.ru Infection (PC + Internet) :
Smartinf.ru may have literally deadly consequences. Its consequences may be even invisible also. Your system might look like a good, neat and properly working system but it might be secretly sending your data and personal details to some one. Some of the major consequences of being attacked by Smartinf.ru on your system as well as on your internet connection is discussed below.
Consequences On PC :
- Degrades the PC performance.
- Unnecessary error messages.
- Excessive boot time.
- Freezing of system which might lead to system crash, etc.
Consequences on Internet :
- Browser hijacking; Its kind of hacking the browser like Firefox, chrome, etc. by changing the homepage setting and URL,thus taking you to some fake and malicious website deliberately.
- Identity theft; Stealing your personal details like credit card number, passwords, etc. online is quite common and Smartinf.ru can easily make you a victim of this.
- Unnecessary and annoying pop ups.
- Fake and malicious emails.
Above discussed are some of the major consequences of Smartinf.ru attack . One may encounter lots of different and even more danger consequences. One should never ignore if any thing unusual happens to the system. To be safe, every one should go for a Smartinf.ru removal tool as soon as any of the symptoms is seen.
Connects to Online Hacker :
Sitting somewhere in the world, may be hundreds or thousands miles away and controlling your entire system's activity is not a big deal for some advanced hackers. They can literally perform magic over the internet rather we should say black magic. You wont even get a single clue and your whole system will be exposed to them.
Hackers some how install Smartinf.ru on you system through internet. Now as you open your system it gets activated and starts capturing your activities. Mostly they target to capture the keys pressed from your keyboard. This is done by an application called keylogger. A key logger is a small application which captures and records all the keys pressed from your keyboard and activities of a system and keeps on sending it to the the host hacker. Hence stealing your each and every password, credit card number, user names and other personal information. This is one of the most common ways to make some one a victim of identity theft and money laundering.
For a common skilled user, it is next to impossible to identify it. Therefore one has to be very careful while surfing internet. One should always go for an automatic Smartinf.ru removal tool in order to be safe instead of manual method because removing Smartinf.ru manually in quite impossible.
Automatic Tool Software Features :
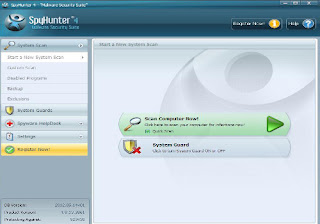
Automatic Smartinf.ru removal tool is very safe and powerful anti-spyware application which protects your system from Smartinf.ru spyware and other with the help of its real time protection. Some important features of this application:
- Quick, complete and custom scanning - It scans your complete hard disk, removable drives, memory, registry, individuals folders etc .
- Detect and Remove - spyware , malware, adware, trojans, worms, keyloggers, hijackers and some other types of threat.
- Real-time Blocking – it provides you the facilities of real-time blocking of threat which prevents your computer from harmful software installation or re- installation.
- Automatic Threat update – fast and continuous threat updates are downloaded and installed automatically which protects your PC from different types of spyware.
- Easy and simple user interface – very interactive and user friendly interface where you can operate the tool without any help.
- Efficient support service : if you are facing the problem when you use the application then you can contact the customer support team where you can get the solution of your problem easily in few minutes.
- Operating system compatibility : it is compatible with the all windows versions like windows 7, win xp, vista, win 97, 98,2000, 2003, windows server 2008.

User Guide- To delete Smartinf.ru infections completely :
Below you can find out few simple steps that states you how to remove Smartinf.ru related infections from affected Windows PC. These steps will guide you throughout the process providing you technical help especially for those who don't have much knowledge about the computers.
Step 1.
First of all download and install the application properly after that open the application. When the main interface of the application will open then you will see the button “Scan computer”. Click on this button to start the scan for Smartinf.ru spyware in your pc.
Step 2.
After finishing the scanning process it will see the list of threats and infected items. When you select any one of them then you can see the details about the infected items and how much it is harmful.
Step 3.
With the help of “Spyware Help Desk ” you can easily find out the details related to the spyware and malware items which is found in your PC.
Step 4.
You can block all infected item with the help of “System Guard” to make you safe from spyware and malware.
User guide to remove Smartinf.ru with Smartinf.ru removal tool :
Step2: If you face any problem regarding installation of the software, either then use anther browser or restart your PC in safe mode with networking
Step3: After you finished installing the Software, scan your PC
Other Search Terms for Smartinf.ru infection
Smartinf.ru , How to remove Smartinf.ru , get rid of Smartinf.ru , steps to delete Smartinf.ru , Smartinf.ru automatic remove. uninstall Smartinf.ru.









No comments:
Post a Comment